This security flaw takes advantage of a system performance optimization function that allows extracting sensitive information from the system. Through a series of commands it is possible to extract data from the FPUs and then use it to obtain specific data of the different applications that the user has in his device.
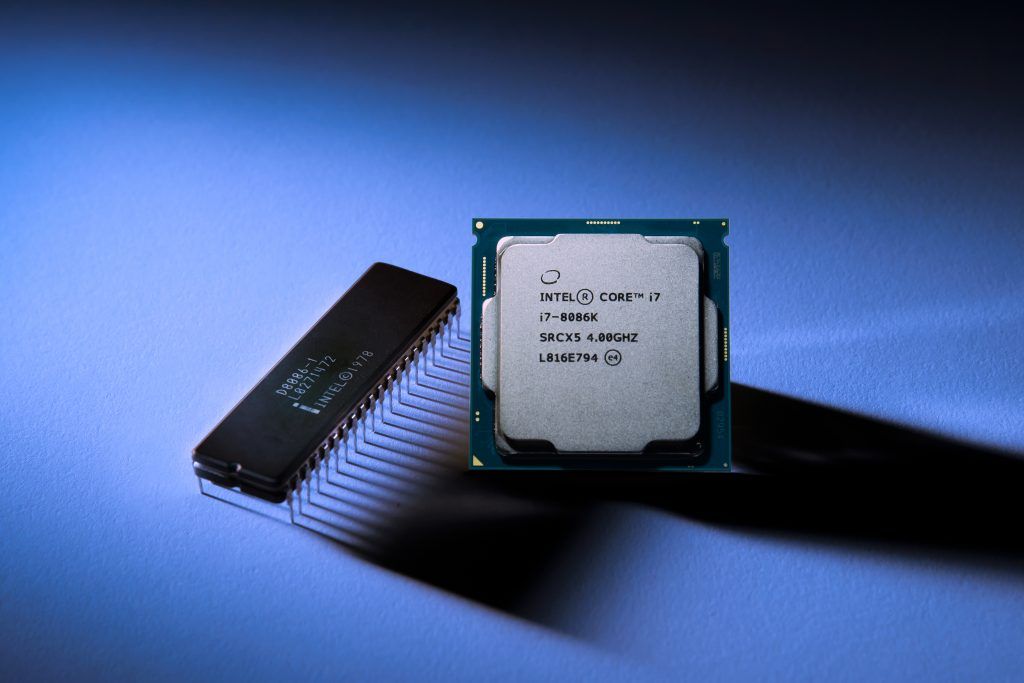
This is a very serious problem given the high number of affected users, all those who have devices with Intel Core and Intel Xeon processors. Being an error in the CPU itself, affects all operating systems that use deferred FPU context switching.
This function is used to optimize performance by saving and restoring the records of the FPU (floating point unit). The failure allows another process to access these records and to extract all the data stored there.
This vulnerability can be addressed with operating system updates. Many Linux and Microsoft distros already have released updates related to this security flaw.
Source: Tecnonucleous






0 Comments